work with Tranquility
on your IT assets
IT asset management with WAPT
Discover how to act simply and efficiently on your entire IT infrastructure.

Self-service
Automate your employees’ autonomy in a single platform.

Silent update
Simplify the deployment of your updates according to your needs.

Package creation
Create and deploy your own packages across your IT estate.
Find the formula best suited to your needs
Our solution has been developed to meet your needs by helping you on a daily basis
The software deployment and asset management solution for Windows, Linux and macOS.

A complete audit of your assets and installation of Samba-AD to secure your IT assets.
Our blog
OpenRSAT — A free, cross-platform alternative to Microsoft’s RSAT
OpenRSAT is a free and open source solution that allows system administrators...
Tranquil IT and open source software: a shared history
Founded in 2002 by brothers Vincent and Denis Cardon, Tranquil IT embodies the...
Tranquil IT and Green IT
In a world where ecological transition has become a priority, the IT sector...
WAPT, in a few steps…
Find out how to take simple, effective action across your entire IT estate.
Keeping your computer installed base up to date with WAPT
To address security flaws and the growing number of software products to maintain in enterprises, we created WAPT. With WAPT, you remotely deploy, maintain and remove software and configurations from a simple to use central management console.
Deploying software with WAPT
WAPT is the perfect software deployment solution for Windows. The WAPT remote management console allows you to install, update and uninstall your software and your configurations on your installed base of workstations. To secure your deployments, you may use ready-to-use packages that you re-sign into your own repository, or create and sign your own packages.
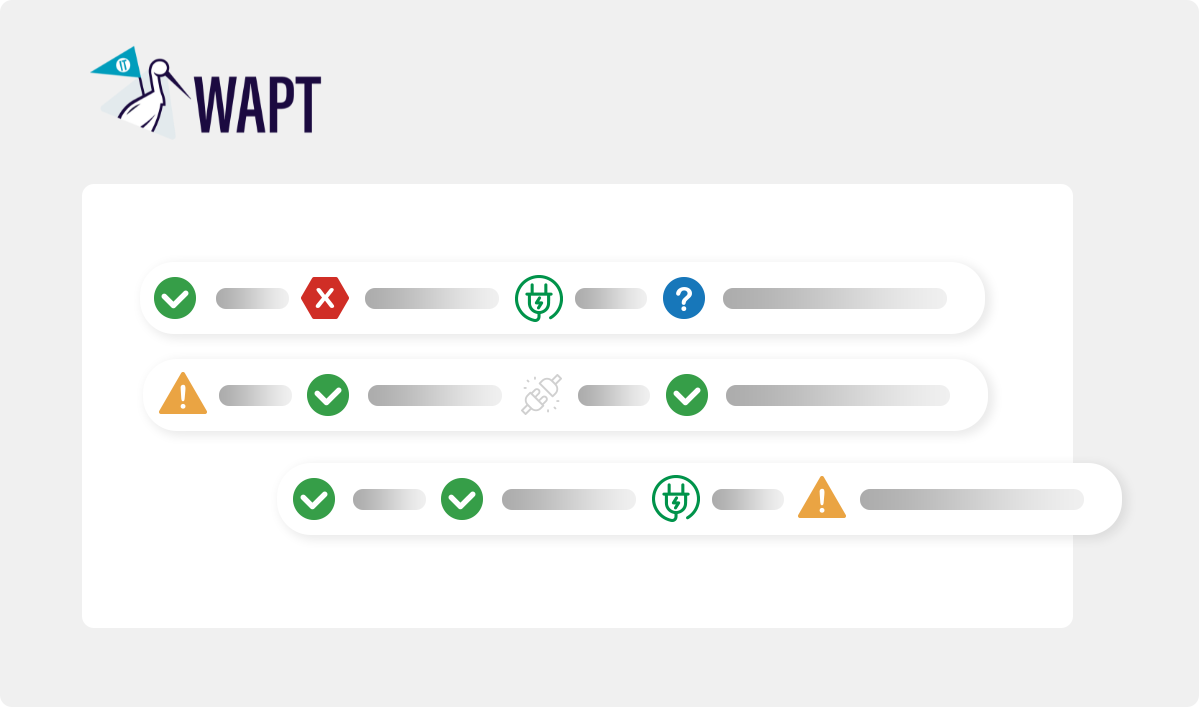
Collecting inventory feedback with WAPT
The correct management of your installed base of workstations goes hand in hand with having a reliable inventory. This is why WAPT allows you to keep an inventory of your machines and their configuration in real time.
More than 300 projects completed, they trust us…





Migrate and track your package deployments with WAPT














