Corporate cybersecurity
WAPT lets you deploy software and patches.
Benefit from software natively designed for desktop security.
Protect your park
WAPT allows you to deploy your solution, secure your fleet and verify its compliance.
Cybersecurity features

WAPT is designed for cybersecurity
The WAPT server is not considered a sensitive asset, as it cannot be used to attack workstations.
The WAPT packages on the official Tranquil IT store have been assembled with the utmost care, using verifiable methods.
The content of any WAPT package is readable by the administrator so that he or she can have confidence in the package’s repercussions on his or her IT estate.
Package deployment modes allow emergency patch deployment on connected workstations.


In WAPT, everything is signed for security
All actions in WAPT are digitally signed which ensures their authenticity and integrity.
Exchanges between servers and agents are secured by the most powerful TLS protocols.
Sensitive data contained in a WAPT packet can be encrypted to ensure confidentiality all the way to its destination machine. Conversely, sensitive data can be sent up from the inventory in encrypted form, and therefore only readable by the machine’s administrator.
Sensitive data can be sent up from the inventory in encrypted form, and therefore only readable by the machine’s administrator.
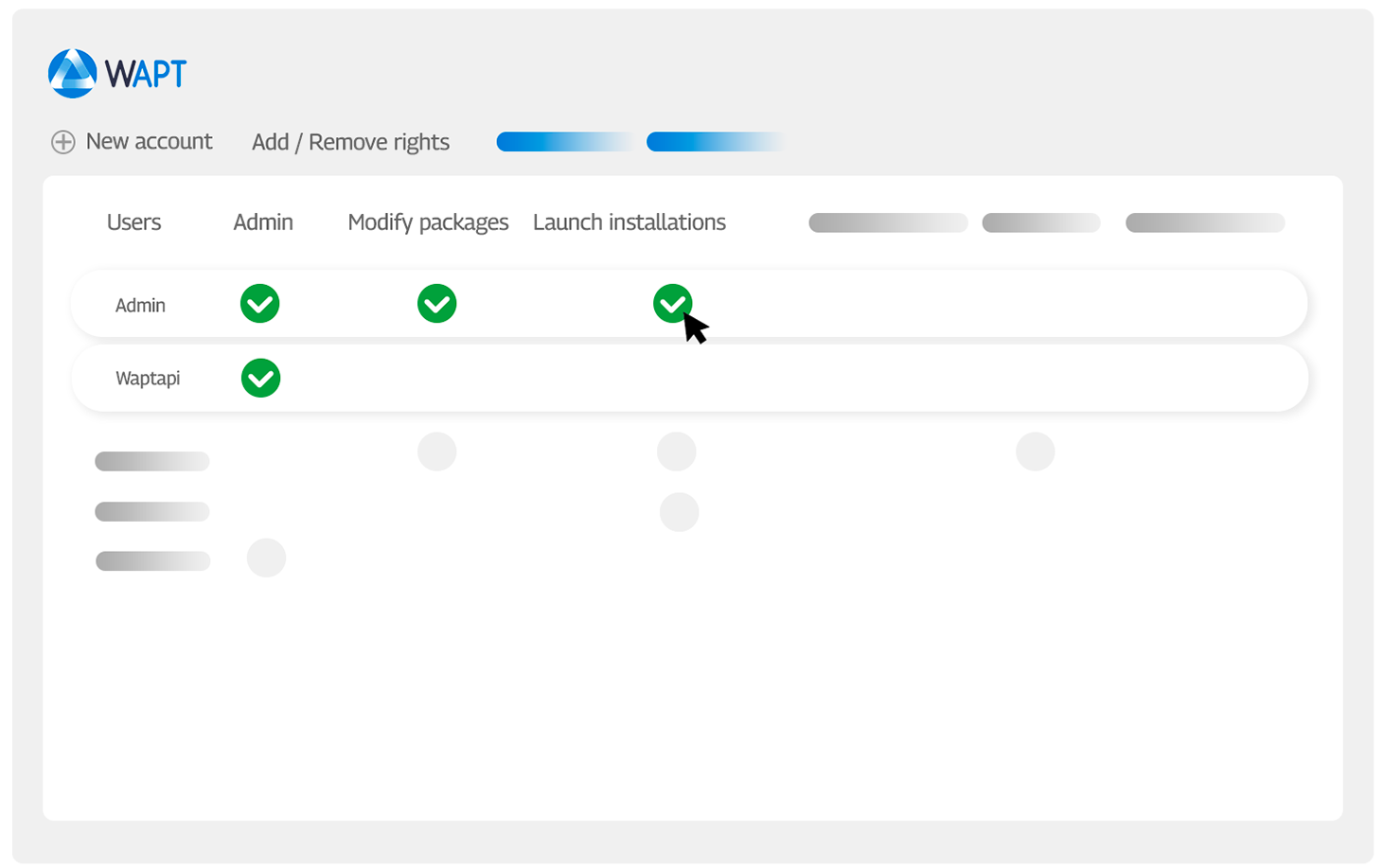
Manage access rights with ACLs
Access Control Lists (ACLs) enable finer-grained management of access rights to WAPT functions by authenticated administrators.

Migrate and track your package deployments with WAPT







