work with Tranquility
on your IT equipment
WAPT, the software deployment and IT asset management solution for Windows, Linux and macOS. > Learn more
SAMBA-AD, the ideal software for managing and securing your IT assets and access to network resources. > Learn more
IT asset management with WAPT
Discover how to act simply and efficiently on your entire IT infrastructure.
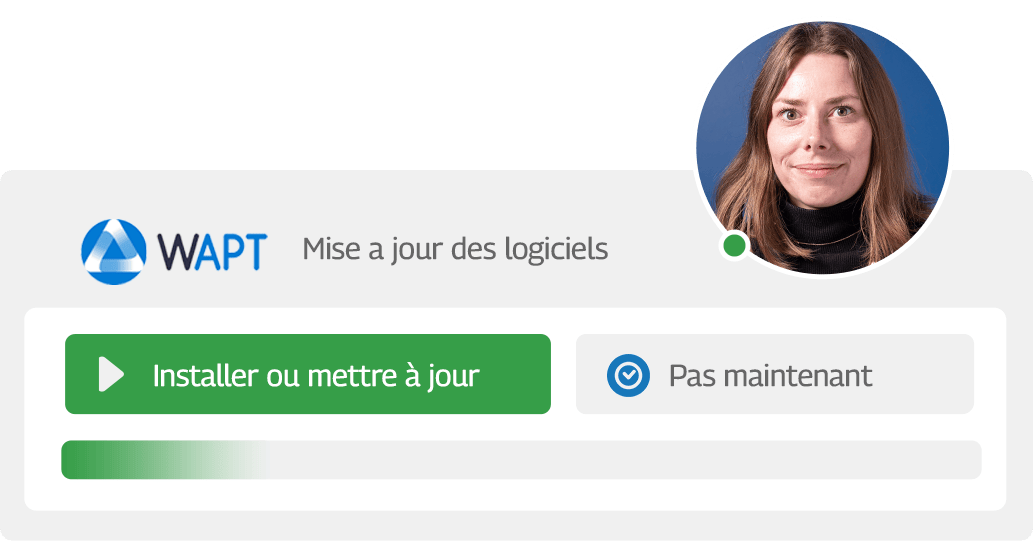
Self-service
Automate your employees’ autonomy in a single platform.
Silent update
Simplify the deployment of your updates according to your needs.
Package creation
Create and deploy your own packages across your IT estate.
Find the formula best suited to your needs
Our solution has been developed to meet your needs by helping you on a daily basis.

The software deployment and asset management solution for Windows, Linux and macOS.

A complete audit of your assets and installation of Samba-AD to secure your IT assets.
WAPT, in a few steps…
Find out how to take simple, effective action across your entire IT estate.
Keeping your computer installed base up to date with WAPT
To address security flaws and the growing number of software products to maintain in enterprises, we created WAPT. With WAPT, you remotely deploy, maintain and remove software and configurations from a simple to use central management console.
 WAPT 1.5 Enterprise version is qualified by the French National Agency for Information Systems Security (ANSSI). The Security Visa guarantees WAPT’s reliability and robustness in terms of security.
WAPT 1.5 Enterprise version is qualified by the French National Agency for Information Systems Security (ANSSI). The Security Visa guarantees WAPT’s reliability and robustness in terms of security.
Deploying software with WAPT
WAPT is the perfect software deployment solution for Windows. The WAPT remote management console allows you to install, update and uninstall your software and your configurations on your installed base of workstations. To secure your deployments, you may use ready-to-use packages that you re-sign into your own repository, or create and sign your own packages.
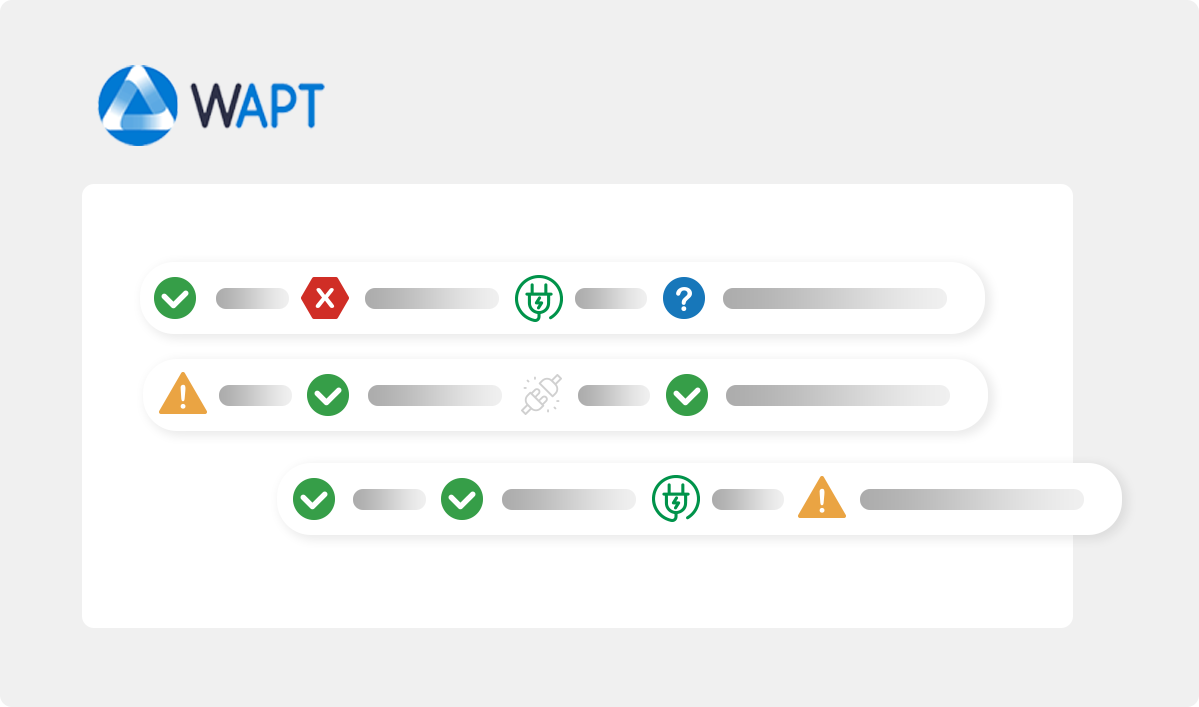
Collecting inventory feedback with WAPT
The correct management of your installed base of workstations goes hand in hand with having a reliable inventory. This is why WAPT allows you to keep an inventory of your machines and their configuration in real time.
The right offer for every sector
 |
|
| « When I did the trial, I immediately saw the results. » Joël LATIEULE, Victor Hugo school IT Manager |
Protect and deploy your solution remotely, depending on the location. I want to learn more |
 |
|
|
“Tranquil IT takes care to follow its customers even beyond the initial specifications. That makes a big difference. Johann LECLERCQ, DRAC Pays de la Loire, IT Manager |
Deploy your solution without any impact on users, securing your on-site or multi-site IT assets. Read more |
 |
|
|
“We were quick to endorse WAPT. Our tests confirmed our choice. It’s a winning bet for CPAM!” Jean-Sébastien PLOIX, CPAM 13 Department Manager |
From a distance, take advantage of simple deployment to facilitate the work of your teams while meeting your security needs. Read more |
 |
|
|
“We have a solution that works, that’s reliable and secure.” Sébastien VOLEAU, SAH Leduc System and network administrator |
Deploy your packages on your aging fleet, while benefiting from reporting on your actions. Read more |
 |
|
|
“I used to maintain my equipment by hand, but now I can configure my workstations from A to Z, and keep an eye on the status of my equipment thanks to the WAPT console. ” Bastien HERMITTE, B2P Web System Admin |
Quickly offer your employees a remotely deployable solution. Read more |
 |
|
|
“I tested the project and found its philosophy very compatible with our operations.” Bastien Travers, Sofia Managing Partner |
Take advantage of a record-breaking value-for-money solution, with software tailored to your structure. Read more |
 |
|
| Discover an offer adapted to your sector. |
If you’re a member of an association or a professional in the social sector, we can help. Read more |
More than 300 projects completed, they trust us…





Our blog
France 2030: Hexagone
The birth of the projectThe French government launched France 2030 in 2021, a project to...
FAQ WAPT 2.5 : Answers to your questions
It's now been several months since the release of WAPT 2.5. Let's take a look at the 10...
WAPT 2.5.2 released: What features does it offer?
After several months of development, version 2.5.2 of WAPT is now available. We wanted to deliver a version that improved the security and performance of WAPT. We’ve used 2.5.2 to add some new features and clean up the code.

Migrate and track your package deployments with WAPT









